搜索结果: 1-15 共查到“sponge”相关记录47条 . 查询时间(0.546 秒)

分子模拟作为一个重要的理论研究手段,可以在微观分子世界与宏观可观测量之间搭建桥梁,从而为人们在分子水平上理解物质的结构和动力学性质提供工具,其在化学化工、生物医药、能源、材料等多个领域都有广泛的应用。虽然近几十年来国际学术界和工业界已发展出很多具有特色的分子模拟软件,如AMBER、CHARMM、GROMACS、LAMMPS、ACEMD和Material Studio等,但是在分子模拟领域国内一直没...
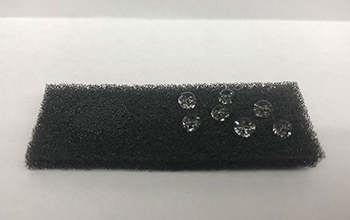
A team funded by the National Science Foundation has developed a porous smart sponge that selectively soaks up oil in water.With an ability to absorb more than 30 times its weight ...
We formalize and analyze the general suffix keyed sponge construction, a pseudorandom function built on top of a cryptographic permutation. The construction hashes its data using the (keyless) sponge ...
Towards Lightweight Side-Channel Security and the Leakage-Resilience of the Duplex Sponge
Authenticated Encryption Duplex Construction Leakage-Resilience
2019/3/1
Authenticated Encryption (AE) has become the de facto standard for encryption in modern protocols, and the ubiquitous deployment of small connected devices naturally calls for the availability of ligh...
Post-quantum security of the sponge construction
Post-quantum cryptography hash functions Sponge construction
2017/8/16
We investigate the post-quantum security of hash functions based on the sponge construction. A crucial property for hash functions in the post-quantum setting is the collapsing property (a strengtheni...
sLiSCP: Simeck-based Permutations for Lightweight Sponge Cryptographic Primitives
Lightweight cryptography Cryptographic permutation Simeck block cipher
2017/8/10
In this paper, we propose a family of lightweight cryptographic permutations called sLiSCP, with the sole aim to provide a realistic minimal design}that suits a variety of lightweight device applicati...
Bacteria living in marine sponge produce toxic compounds found in man-made products
Bacteria living marine sponge toxic compounds man-made products
2017/7/20
Researchers have discovered for the first time that a common marine sponge hosts bacteria that specialize in the production of toxic compounds nearly identical to man-made fire retardants, a finding t...
Study Finds Bacteria Living in Marine Sponge Produce Toxic Flame Retardant-Like Compounds
Bacteria Living Marine Sponge Produce Toxic Flame Retardant-Like Compounds
2017/7/20
A Scripps Institution of Oceanography at the University of California San Diego-led research team discovered for the first time that a common marine sponge hosts bacteria that specialize in the produc...
Collapsing sponges: Post-quantum security of the sponge construction
quantum cryptography hash functions
2017/3/31
We investigate the post-quantum security of hash functions based on the sponge construction. A crucial property for hash functions in the post-quantum setting is the collapsing property (a strengtheni...
Conditional Cube Attack on Reduced-Round Keccak Sponge Function
Keccak-MAC Keyak cube tester
2016/12/10
The security analysis of Keccak, the winner of SHA-3, has attracted considerable interest. Recently, some attention has been paid to the analysis of keyed modes of Keccak sponge function. As a notable...
A Robust and Sponge-Like PRNG with Improved Efficiency
sponge pseudo-random number generator (PRNG) Patarin's H-coefficient technique
2016/12/9
Ever since Keccak won the SHA3 competition, sponge-based
constructions are being suggested for many different applications, including
pseudo-random number generators (PRNGs). Sponges are very
desir...
We present the Bash family of hashing algorithms based on the sponge paradigm.
A core element of this family is the Bash-f sponge function which refers to the LRX (LogicalRotation-Xor)
class of symm...
We study the problem of devising provably secure PRNGs
with input based on the sponge paradigm. Such constructions are very
appealing, as efficient software/hardware implementations of SHA-3 can
ea...
Practical Complexity Cube Attacks on Round-Reduced Keccak Sponge Function
Keccak SHA-3 sponge function
2016/1/23
In this paper we mount the cube attack on the Keccak sponge function. The cube attack, formally introduced in 2008, is an algebraic technique applicable to cryptographic primitives whose output can ...
Beyond 2^{c/2} Security in Sponge-Based Authenticated Encryption Modes
Authenticated encryption CAESAR Ascon
2016/1/9
The Sponge function is known to achieve 2^{c/2} security, where c is its capacity. This bound was carried over to keyed variants of the function, such as SpongeWrap, to achieve a min{2^{c/2},2^kappa} ...

